Тема: WiaTag iOS — How To Manage System Restrictions and Control Application
Dear WiaTag users,
Many of you ask how to prevent users from misusing the application. Let’s today speak of the settings on the iOS devices that would help you with the task. Information on Android will be presented in a separate post
In this tutorial we will show you how to:
- prevent users from deleting the application
- compromising application’s permissions
- set a password for changing the restrictions settings
- set up additional messages and parameters for better understanding the usage of the application.
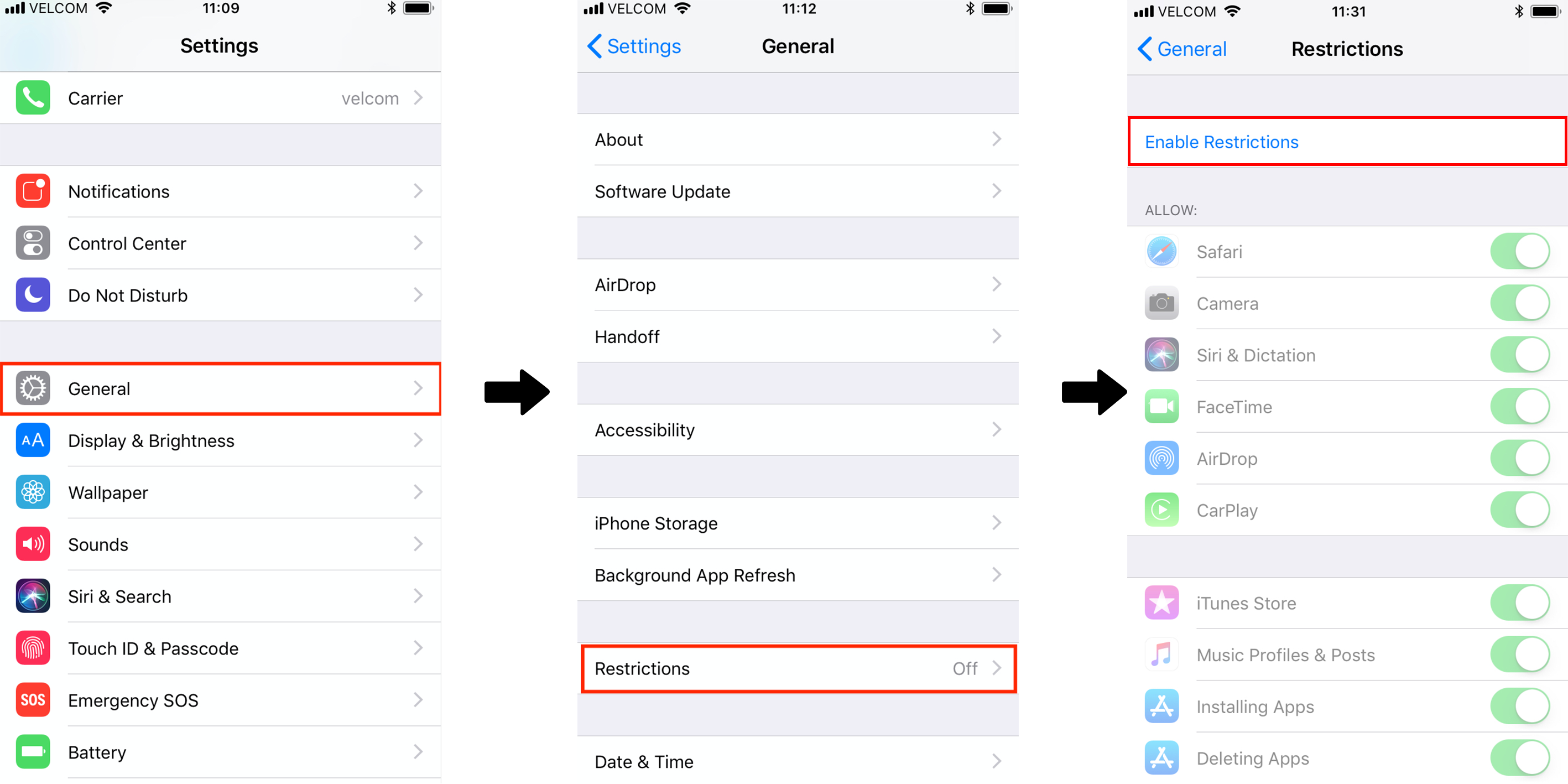
To accomplish the first two points, we will need to enable Restrictions in device’s settings:
Once you have done that, you will need to set a password (and remember it ![]() )
)
Now, we are ready to set the needed restrictions:
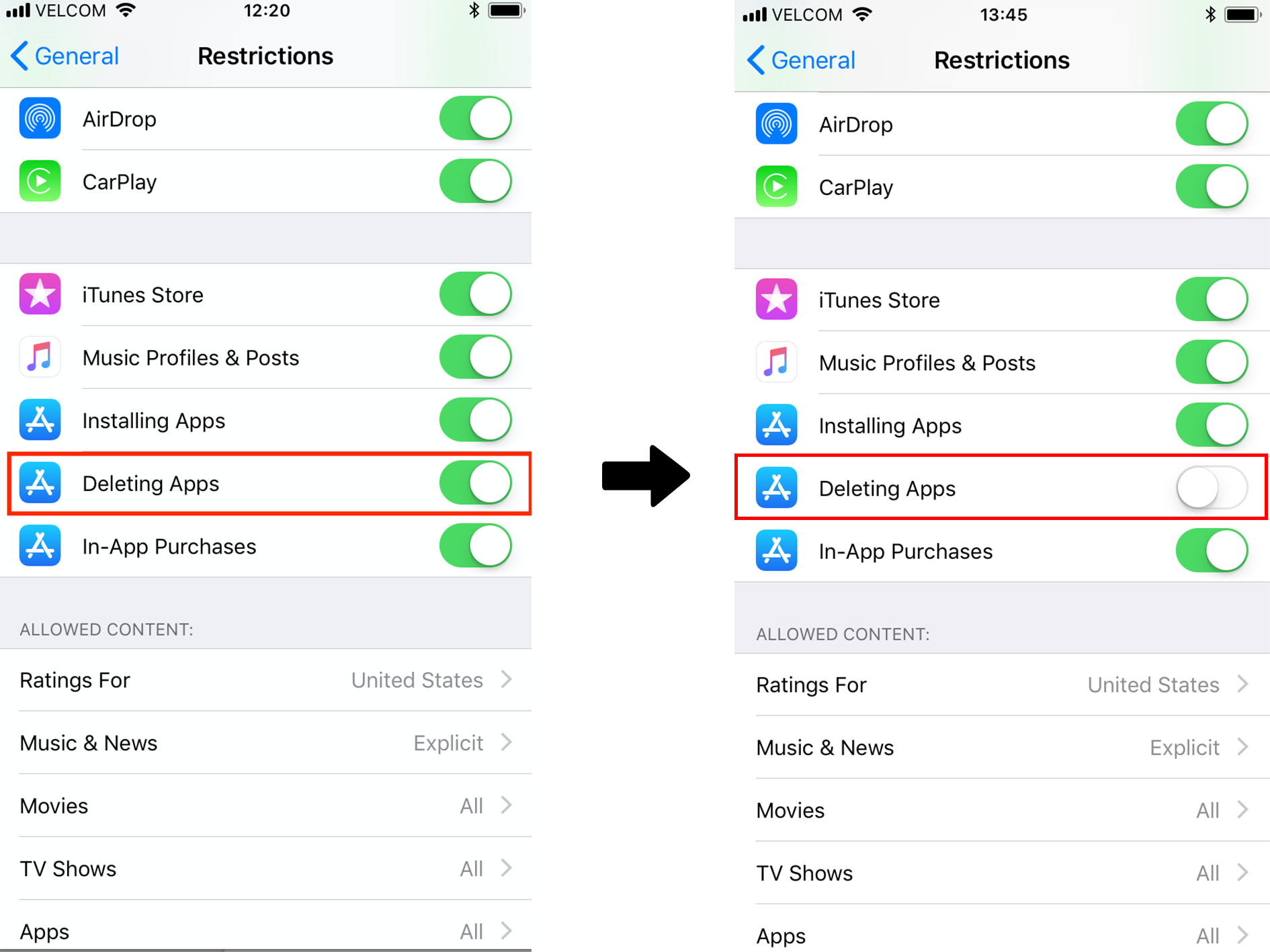
Disable deleting apps:
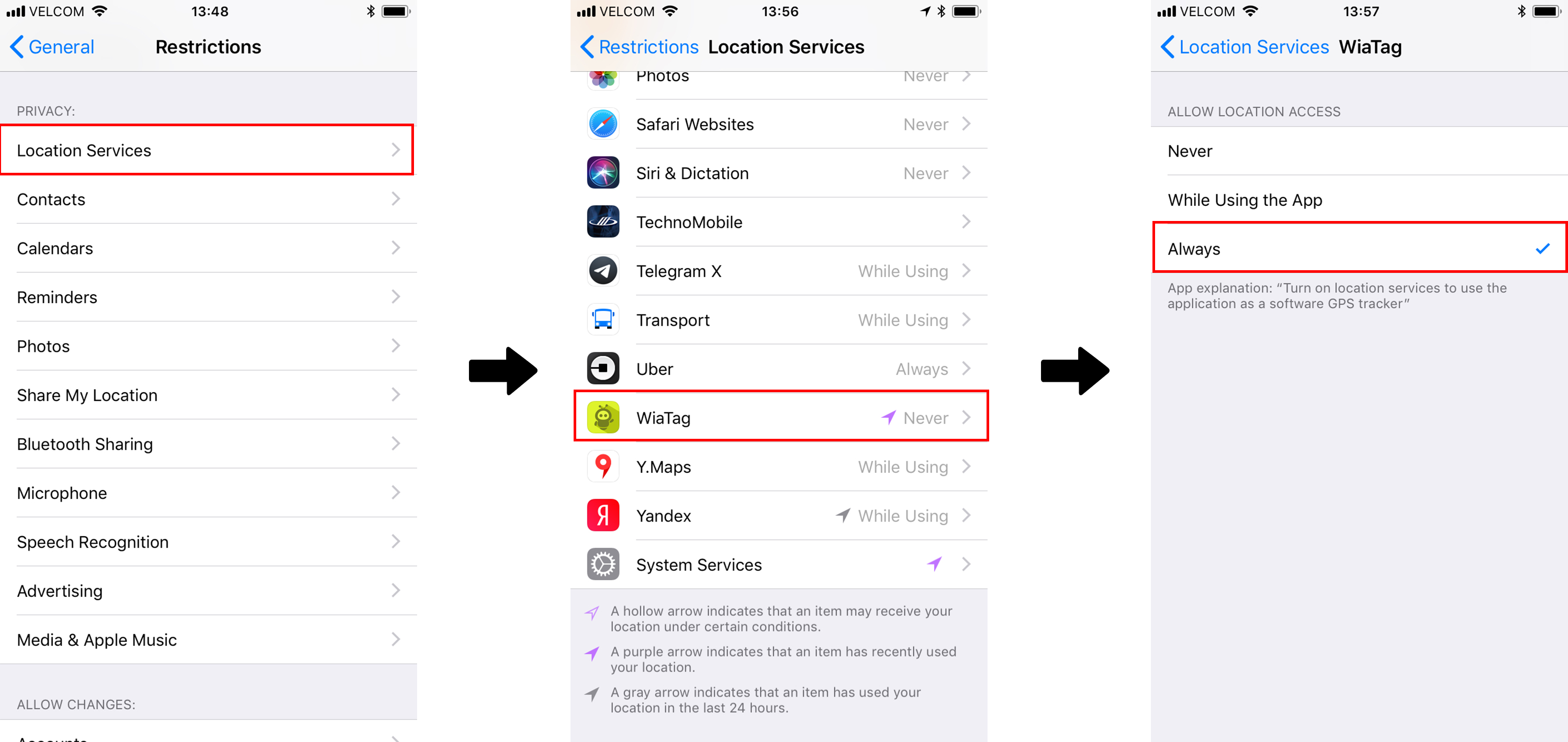
Make sure that location services are allowed in the app:
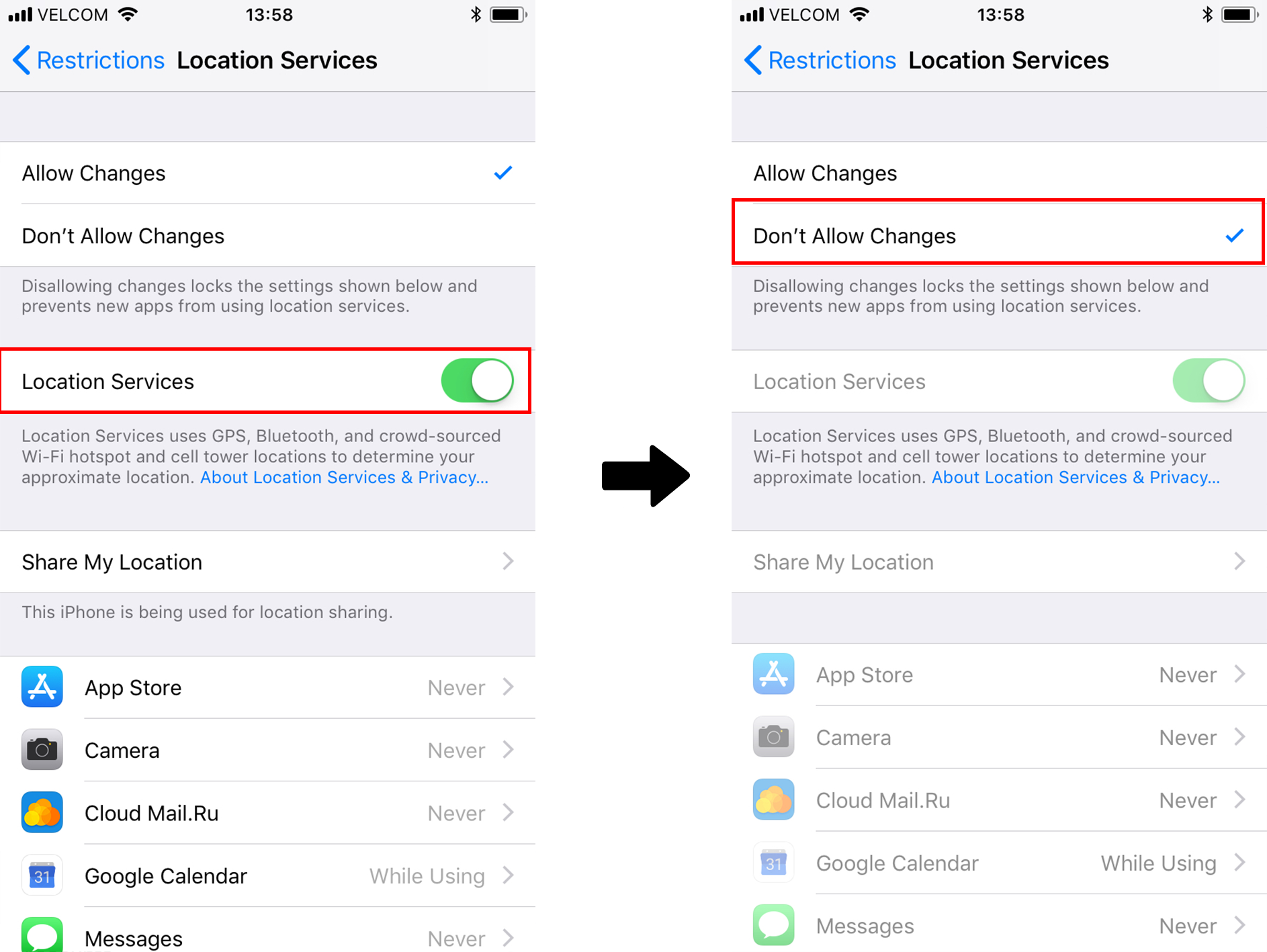
Make sure that location services are on and disable turning them off:
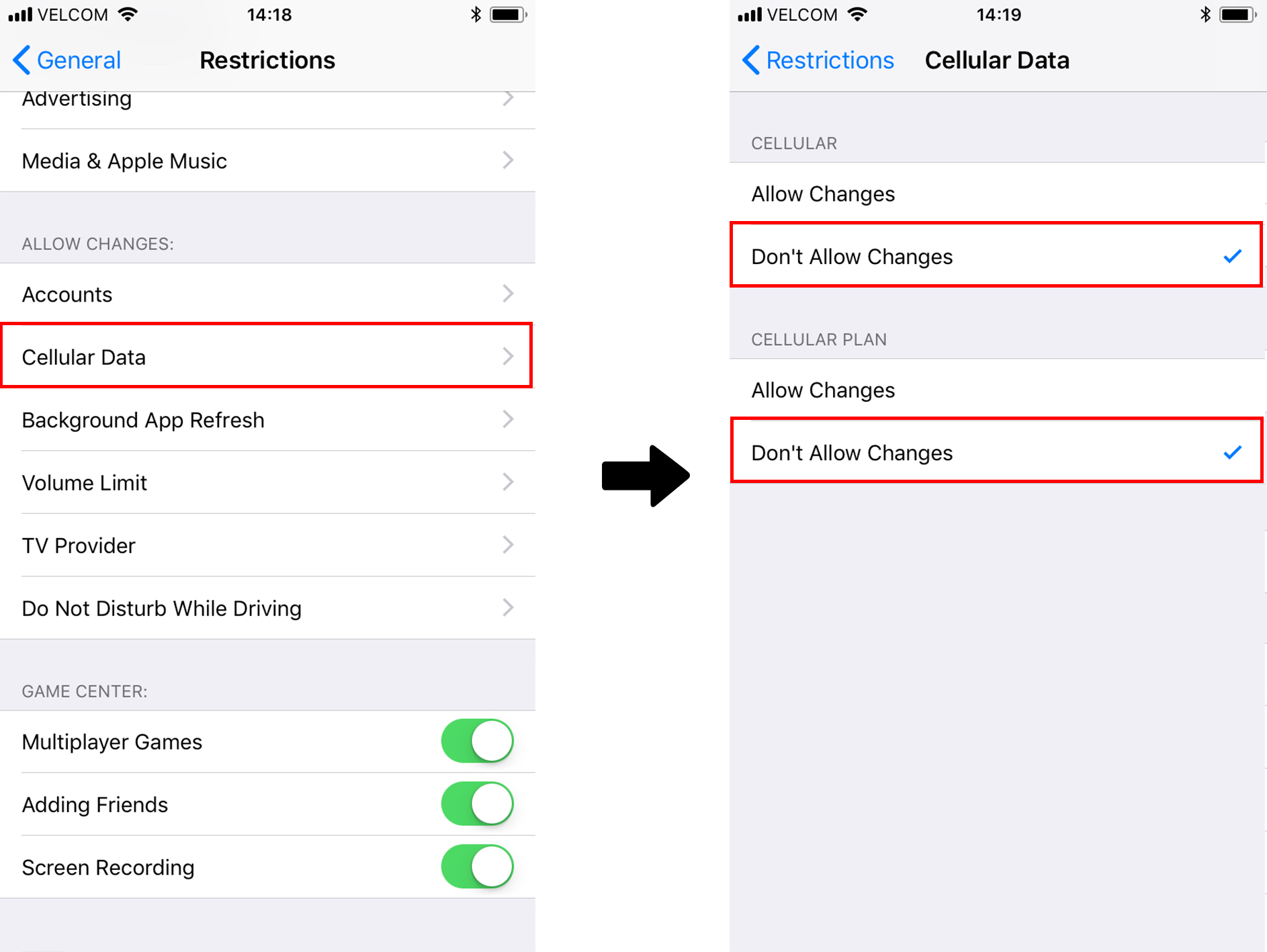
Make sure the user does not turn off cellular data:
In General -> Background App Refreshments make sure Background app refresh is turned on, and the setting is applied for WiaTag. Correct work of Remote Control and Chat depends on this setting
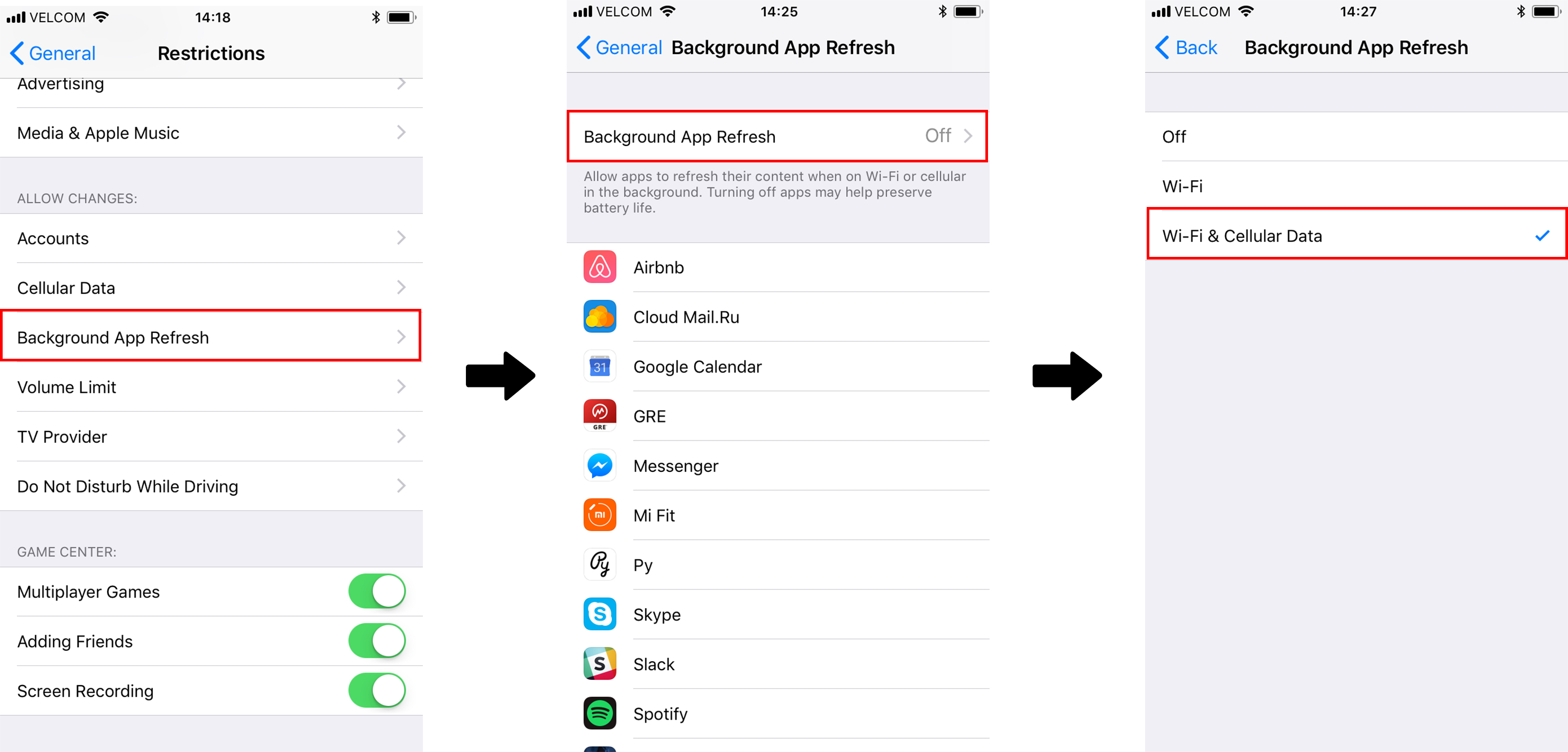
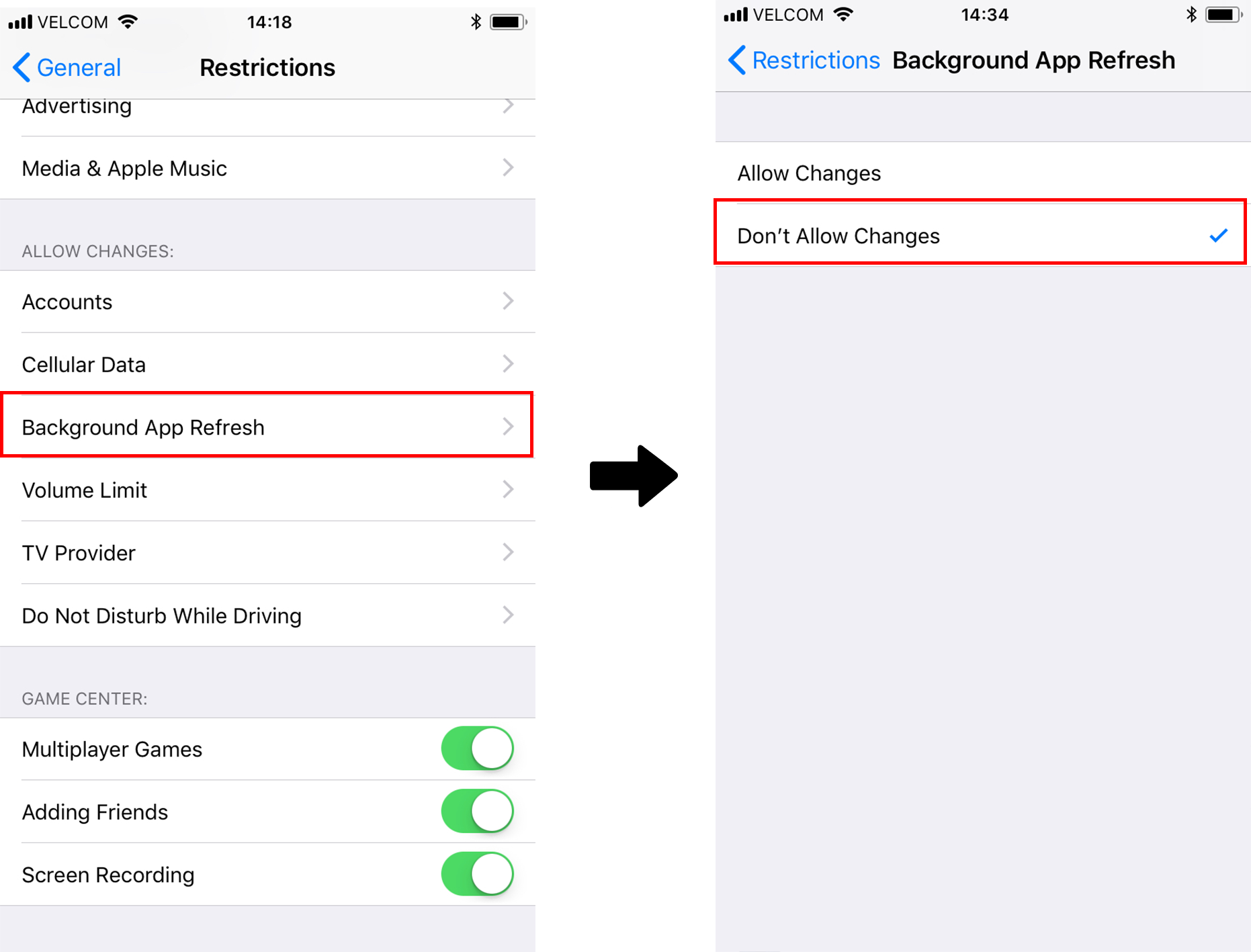
Next, make sure the user is not allowed to change the settings of Background App Refresh in Restrictions:
In a similar fashion, one might limit permissions to any other functionality of iOS settings restrictions.
There is another way to learn about the usage of the application.
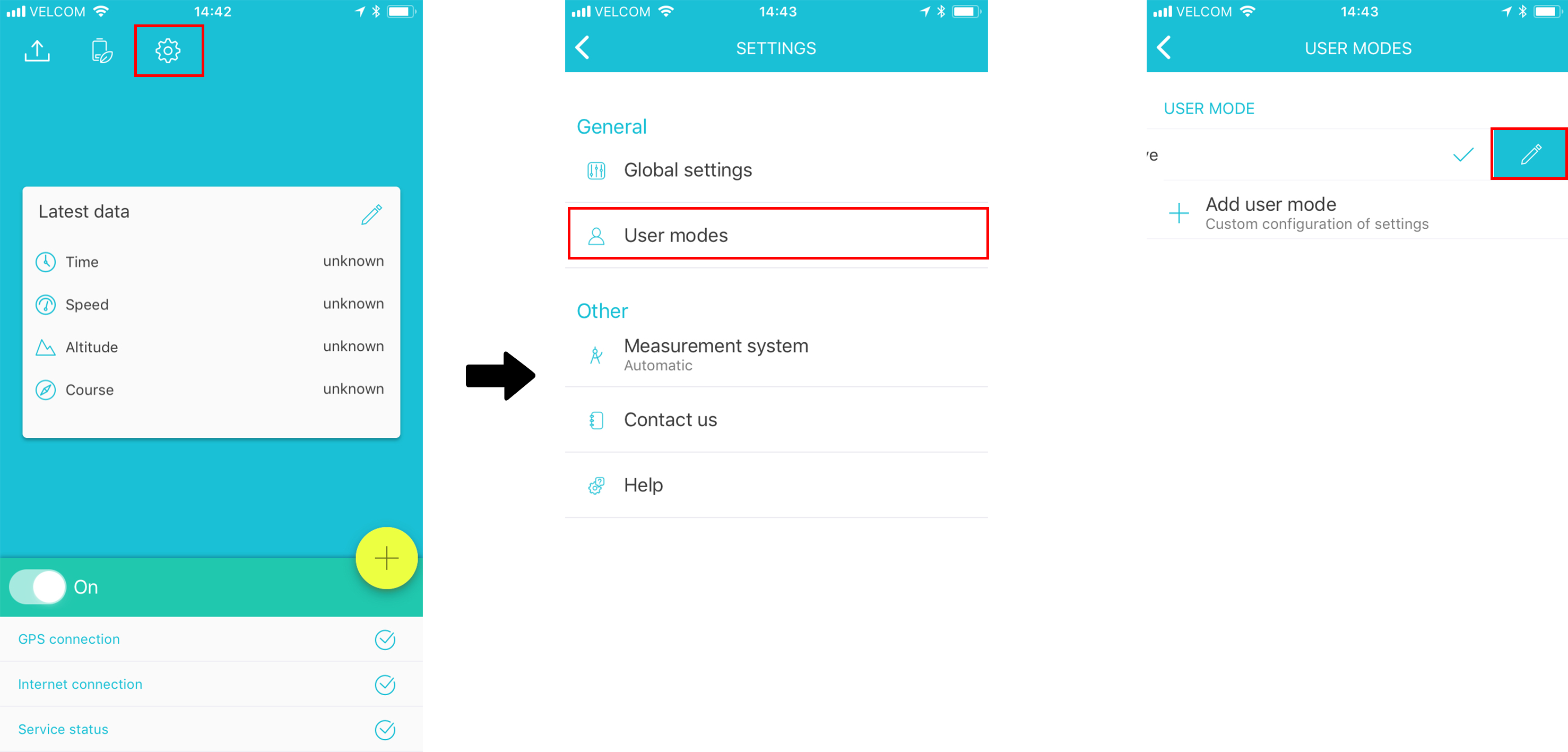
You may turn on sending additional parameters with the positional messages inside the WiaTag application. The setting is well hidden in the layers of the settings, hence, here is an instruction where to find it:
Settings —> User mode —> Swipe left, edit
In Additional parameters, you may find a whole lot other flags that would be sent to Wialon.
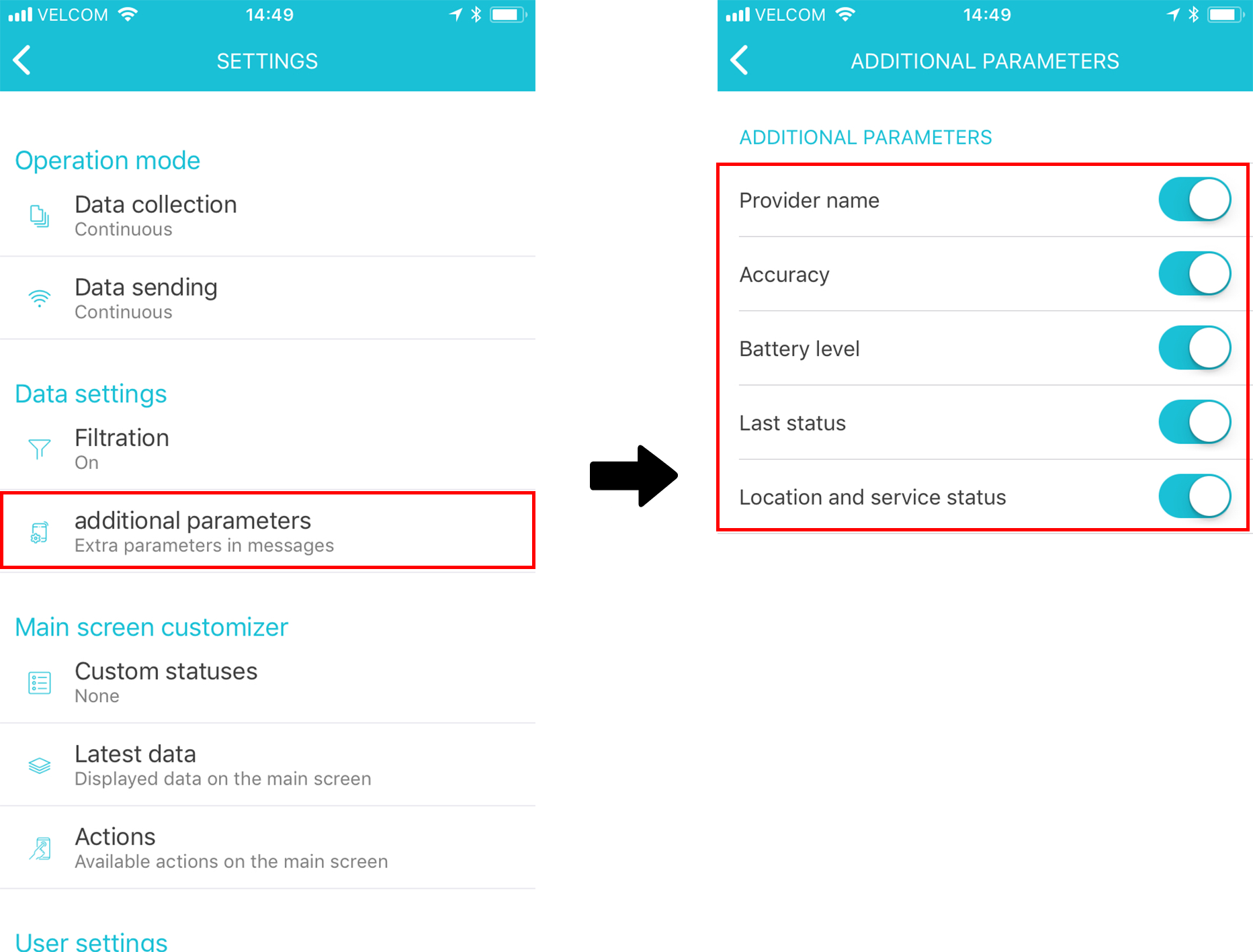
Here, I would be willing to draw your attention to Location and service status — this setting will send you a separate message once the application was launched after the crash, once the location services were disabled for the application or for the device and when the user turns on and turns off the service on the main screen of the application.
Please, remember that none of is a bullet-proof from compromising, and the curious minds will always find their ways to cheat the system. Hence, in our opinion, the best tactics are not to punish for the misbehavior, but the reward for the correct actions.
Would be happy to answer any remaining questions here or at p.bushuev@gurtam.com
Product Owner, Mobile
Gurtam
